If you are using your casual browser, instead of the built-in Burp Suite browser, the first thing you have to do is to import the Burp certificate. This can be easily done by downloading it from the http://burpsuite and installing it according to your browser instructions.
But what if your certificate is in place and you are getting a blank page by using Burp Suite proxy?
This can be antivirus fault.
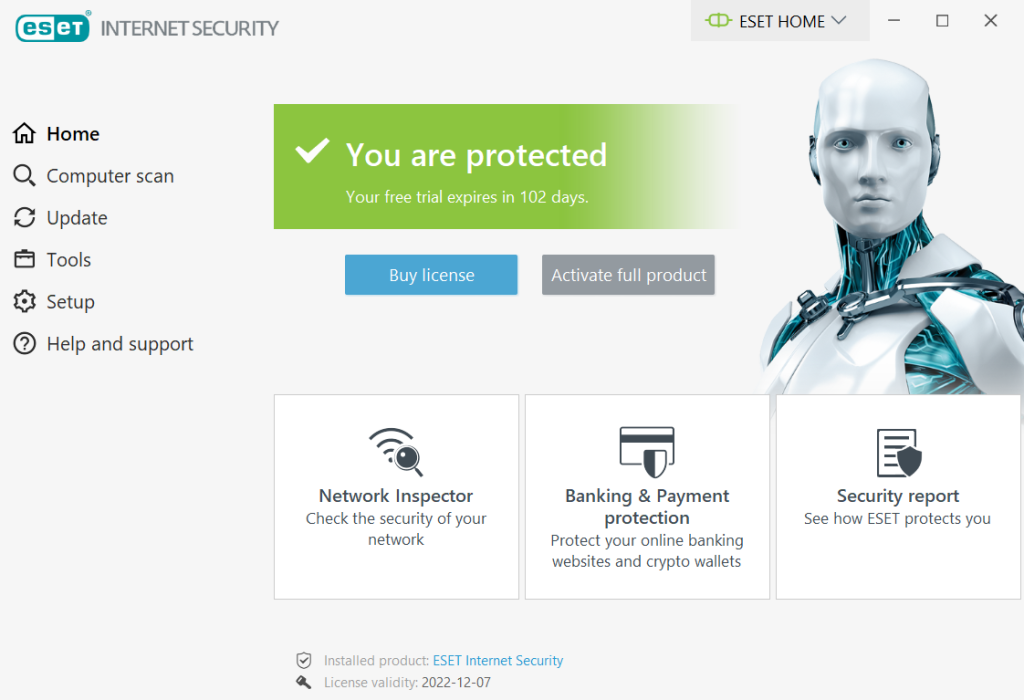
Antivirus software usually provides some kind of web protection. For example, ESET Internet Security, has a Network Attack protection (IDS), that prevents network attacks.
And the thing is, by using Burp Suite, you are basically executing a MiTM attack. So, the antivirus blocks the “attack”.
This is how you can fix the the Burp Suite blank page if you are using Windows and ESET antivirus.
Open the ESET Internet Security dashboard:
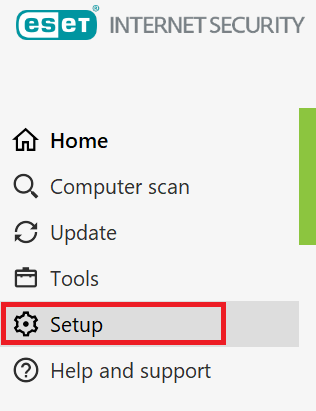
Go to the Setup:
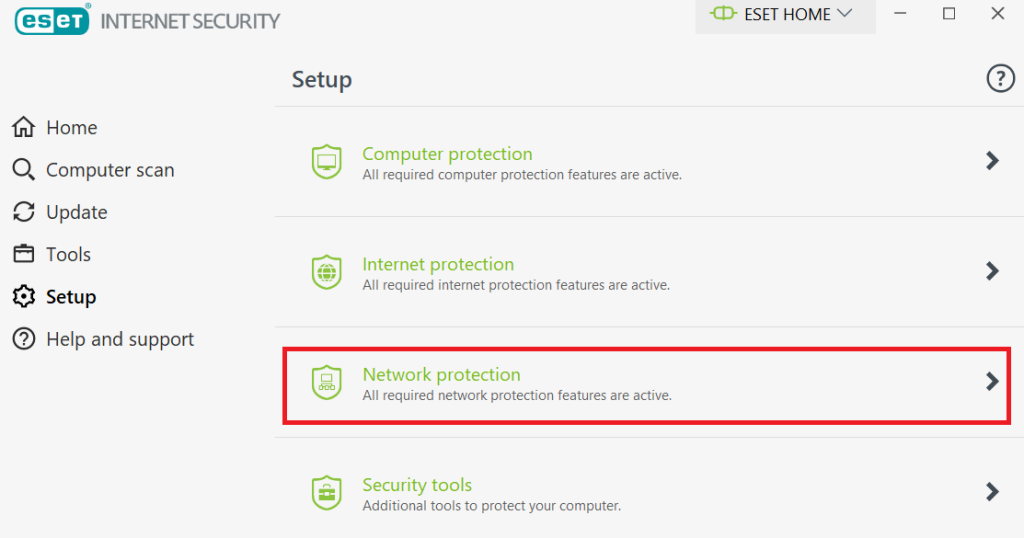
Choose the Network protection:
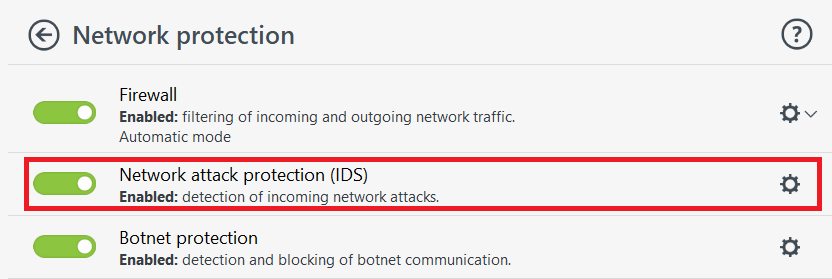
Choose the Network attack protection (IDS):
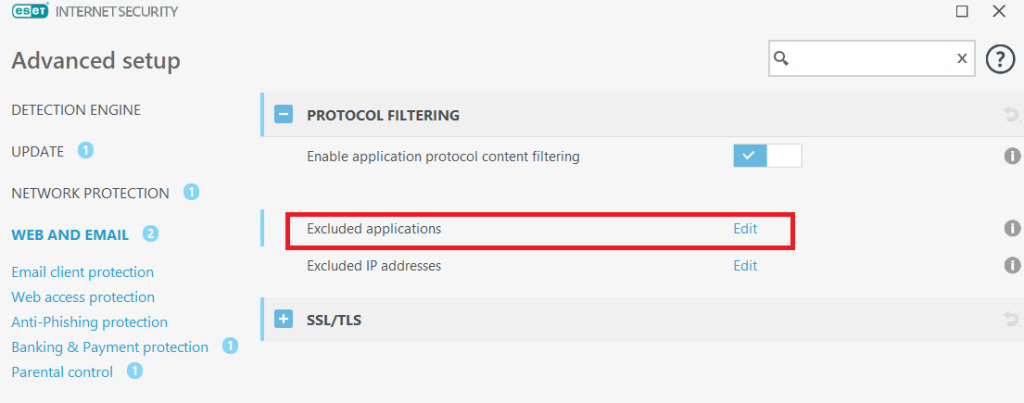
Now in the opened page, choose the Web and Email, and expand the Protocol Filtering settings. You will see the Excluded applications option. Click Edit:
A list with exclusions should open:
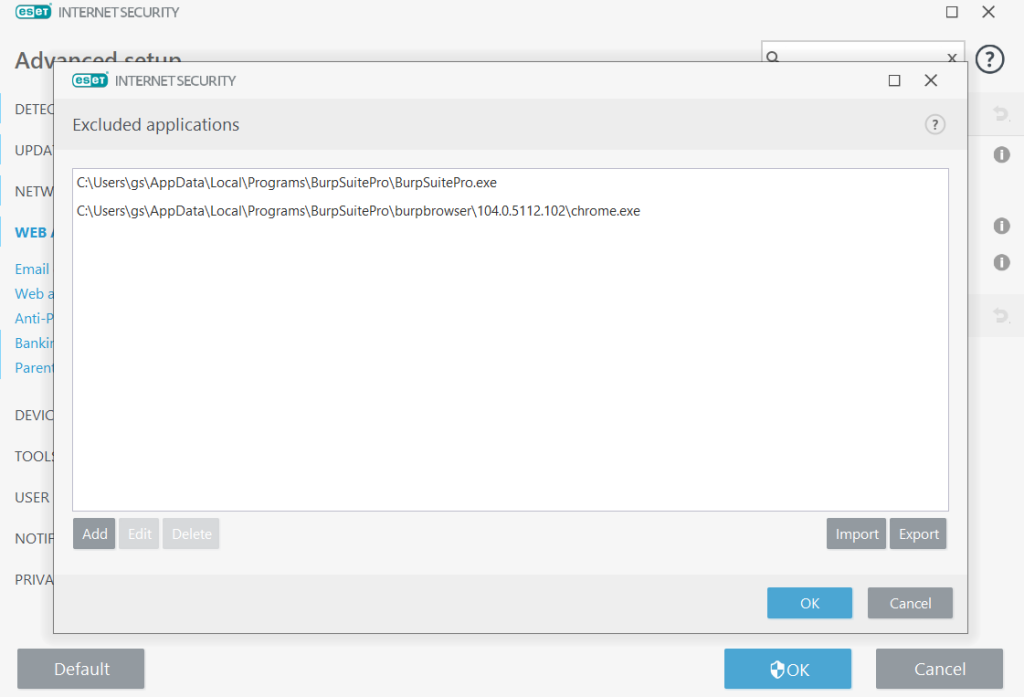
What you should do next, is to make the exclusions for the two applications: Burp Suite, and Burp Suite embedded browser.
Locate where is the Burp Suite installed, and copy the path of Burp Suite executable, and the embedded browser executable.
In my case they were located in the AppData\Local\Programs\BurpSuitePro directory:
- C:\Users\gs\AppData\Local\Programs\BurpSuitePro\BurpSuitePro.exe
- C:\Users\gs\AppData\Local\Programs\BurpSuitePro\burpbrowser\104.0.5112.102\chrome.exe
Probably the easiest way to find where is the Burp Suite in your system, is to search for the Burp Suite shortcut, right click on it, and check what is the path in the properties.
After making the exclusions, you should not get the blank page on the embedded browser of the Burp Suite anymore.
NOTE: keep in mind that in the Chrome browser, that is built into Burp Suite, is stored in the folder called by the version number. This time we whitelisted the browser that is located ..\burpbrowser\104.0.5112.102\chrome.exe, but after an update, the version will change, and the URL might be ..\burpbrowser\105.0.5195.54\chrome.exe or any similar. So, after every update, you will have to repeat the process and edit the path you’ve previously whitelisted.
That’s it. Hope it helped you!

Highly passionate about cyber security (penetration testing, bug bounty hunting, cybersecurity in general), and blogging. I am experienced in vulnerability assessments, penetration testing, various security audits, had worked with various clients, most of them were in finance sector.
CompTIA Security+, CEH, CEH Practical, CEH Master, and OSCP certified.

