If you are a bug bounty hunter, you know that a reconnaissance is utmost important task. How good your research is, will greatly define success on the bug bounty program. You might spend hours testing a system just to find that one vulnerability. But what if one obvious one was always under your nose? What if secret was leaked in the past, and this information is easily accessible? To ensure you won’t end in this situation, there is a tool – Waybackurls.
By the time of writing this post, tool has over 1.7k stars on GitHub, so it is popular between bug bounty hunters.
Let’s see what it can offer.
Simple Command Line Tool to Fetch Historical URLs
Sometimes it does happen that sensitive or technical information was displayed in the past. Usually, it is just a matter of time when the system maintainers notice it. Especially if a really sensitive information is exposed
Unfortunately, internet does not forget anything. And if the webpage was there for enough time, it might be cached by services, such as Wayback machine.
Using the website might be clumsy, and it takes more time, than entering a command in terminal. If you are hacker, you are probably used to the terminal. This is where the Waybackurls comes.
It is not an official WayBack machine CLI, but it is using the official API. The tool was built by the well-known person in cyber community – tomnomnom.
How to Install Waybackurls on Kali Linux
If by any chance you do not have the Golang installed on Kali Linux, you should do so.
It is the only requirement needed for the Waybackurls. Besides this there are many other great ethical hacking tools built with Go, so having the Go compiler opens you many possibilities.
Great news it’s pretty easy to install Go on Kali Linux:
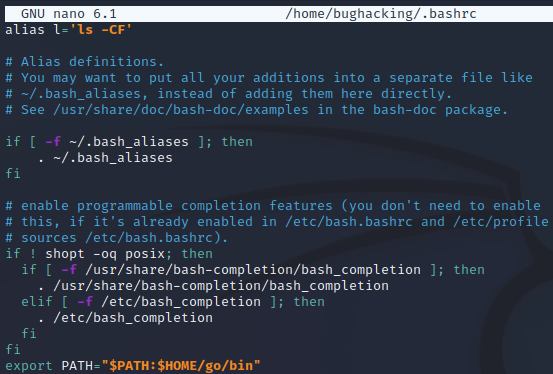
sudo apt install golang-goYou can confirm the installation by command “which go”. As a result path to the Go should be displayed. Another thing you should do, is to add Go to the path. Open the .bashrc file:
sudo nano .bashrc
And append the following line – export PATH=”$PATH:$HOME/go/bin”.
The next step would be to install the tool itself:
go install github.com/tomnomnom/waybackurls@latestIf everything went fine, you should be able to check the help menu:
waybackurls -h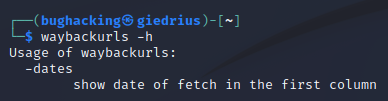
It is really easy to use it. Waybackurl has only one command:
waybackurls example.com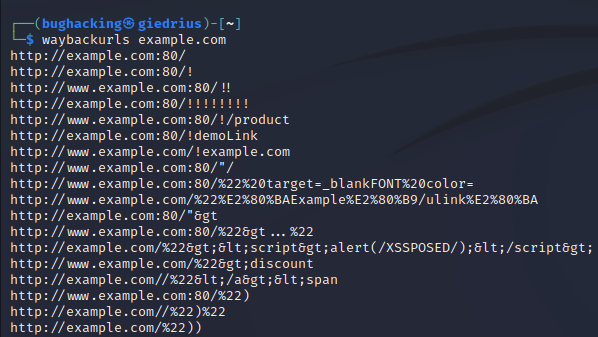
As soon as the command execution finishes, you should get the URLs identified from the Wayback machine.
And if you have a list of hosts and are performing large scale Wayback machine check, load the hosts from file:
waybackurls filenameAre There Any Waybackurls Alternatives?
There surely are.
The tool, as the Tom Hudson states in the GitHub repository of Waybackurl, was inspired by another script written in Python.
And the tool we are covering, became an inspiration for another tool – getallurls (gau). This tool is more powerful, as it is able of fetching URLs from AlienVault’s Open Threat Exchange, Wayback Machine, and Common Crawl.

Highly passionate about cyber security (penetration testing, bug bounty hunting, cybersecurity in general), and blogging. I am experienced in vulnerability assessments, penetration testing, various security audits, had worked with various clients, most of them were in finance sector.
CompTIA Security+, CEH, CEH Practical, CEH Master, and OSCP certified.

