Have you ever wanted to become a samurai of cybersecurity? These elite Japanese warriors were the best in their craft. They were very respected and well paid. While the samurais are gone long time ago, the term has emerged into our modern society. And someone, who has insane cybersecurity skills could be called a samurai. But to reach that level you must learn many things, And one of the things that you might help you to grow, is the OWASP SamuraiWTF project.
This is not another vulnerable application, it is a framework for learning. It means that you can use it to increase your cybersecurity skills. Keep reading to learn how you can become a samurai.
What is the SamuraiWTF?

SamuraiWTF is a project of OWASP (you can see a wasp in the logo of Samurai). The name might sound funny, but it actually has a meaning. WTF is an abbreviation for Web Training Framework. It provides you an environment where you can train on various vulnerable applications. It comes prepacked with all the necessary tools. The framework itself is based on Ubuntu-based basebox, and is pretty lightweight
The project was born in 2008. At the time it was an environment with tools beneficial to web application penetration testing. However, over the time project evolved, and the original creators started focusing on a training environment. Since 2016 code of the Samurai Web Training Framework was migrated to GitHub and it became known as a training framework.
In a way, it can be called as a pentesting operating system.
When it comes to the vulnerable applications the framework supports, you can install some of the popular ones:
- DVWA
- OWASP Juice Shop
- Mutillidae
Also you can install some of the most popular tools easily:
- SQLMap
- OWASP Zed Attack Proxy
When it comes to installing the SamuraiWTF, there are several ways:
- It can be done by using a Vagrant – virtualization solution for building virtual environments. Comprehensive steps will be explained in the following subsection.
- You can download a VirtualBox image. Here is the link: https://tiny.si/samurai
- Booting it up in the AWS infrastructure. This is handy when you want to access framework from across the internet. In order to create it in the AWS, firstly you need to create a workspace with at least 4 GB of RAM and 20 GB of storage. Secondly, you should execute bootstrap.sh script located at the samuraiwtf/base/amazon-linux of the cloned repository.
What is also worth covering, is what’s inside the framework. It comes with a Katana – package management tool. You didn’t expected that a samurai won’t have a katana, did you? This tool can be used for setting the labs and vulnerable applications, also for installing tools for hacking.
How to install SamuraiWTF with Vagrant
The process of installing Web Training Framework is pretty easy. However, make sure you have the necessities: Vagrant, VirtualBox, and GIT (for cloning a repository). There is how you can install the Vagrant (it works on macOS, Windows, and Linux), and here is the VirtualBox download page.
NOTE: If you are installing Vagrant on Windows, you will need a system restart.
When you have everything ready, it is time to clone the SamuraiWTF repository and start installation process:
git clone https://github.com/SamuraiWTF/samuraiwtfAfter the cloning change yourself into the Samurai directory:
cd samuraiwtfAnd run the Vagrant:
vagrant upAfter a moment, the magic should start. The Vagrant should install SamuraiWTF.
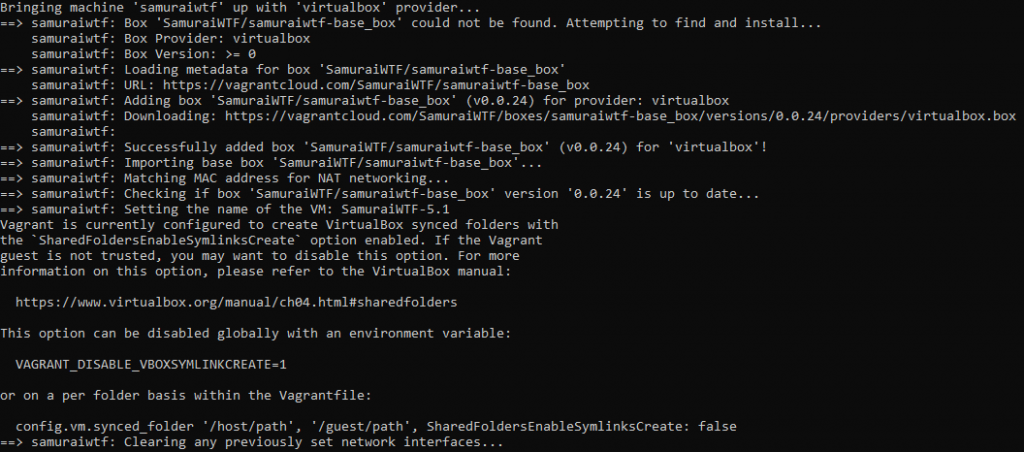
You can open the VirtualBox and you will see that there is a new virtual machine. It has a name of SamuraiWTF-5.1.
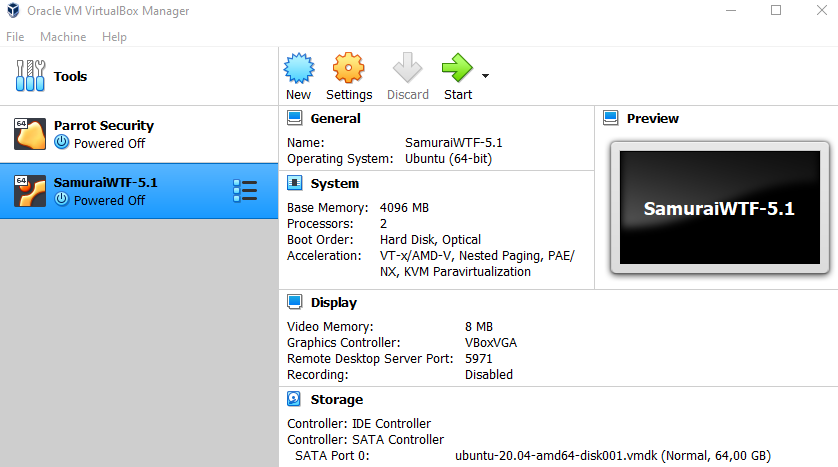
As it is already installed, you may start it and check if everything is all right.
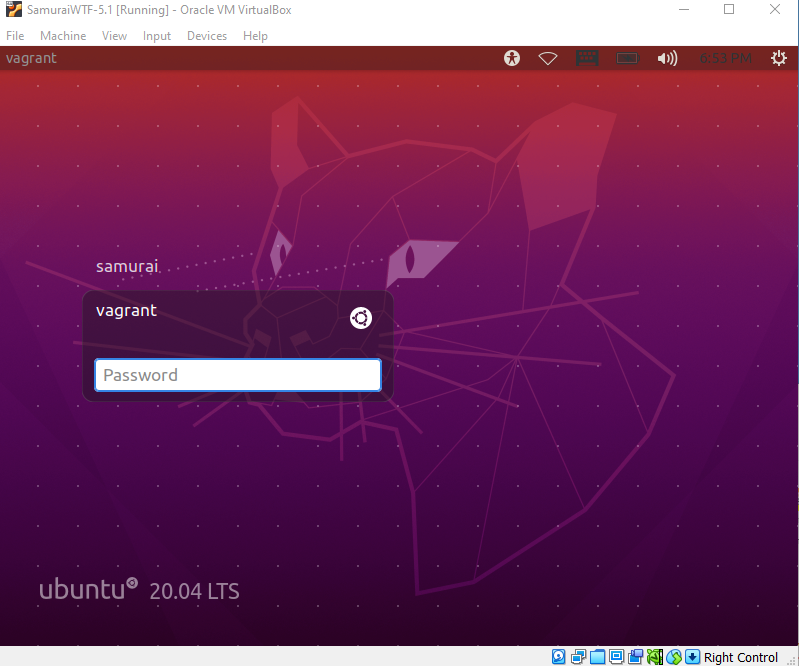
After a boot up you should see a default Ubuntu login window. As the framework runs on Ubuntu, you should feel very familiar with it. Now click on the user samurai, and enter the password.
The default username and password for the SamuraiWTF is samurai:samurai.
That’s it. Now you are ready to start learning.
First Steps With the Samurai Web Training Framework
After starting the SamuraiWTF you will see that it is pretty empty. Under the Applications section of menu there are only basic ones.

But this is actually an advantage, as because of this, SamuraiWTF VM is light. There aren’t unnecessary tools that you won’t ever use.
That’s why there is Katana – a package management tool. When it comes to it, you can easily use it for:
- Listing available tools and applications
- Installing or removing wanted tool or app
- Starting or stopping applications and tools. You can also check its statuses and you can lock them

By using the command katana list you can review what applications and tools are available. You can choose of the most popular vuln apps: Samurai Dojo, Arrrspace, DVWA, Mutillidae, Juice Shop, Musahi.
And of course, tools needed to train with are included in the Katana repository:
- Docker (used by many of the SamuraiWTF targets as conteinerization solution)
- Amoksecurity (domain for hosting payloads)
- OWASP ZAP (one of the scanners and intercepting proxies for web apps)
- Burp Suite (commercial equivalent to ZAP. Has much more functionality)
- Nikto (web scanner)
- SQLmap (tool to search for SQL injections)
- Postman (tool for testing APIs)
- And finally – wordlists that you might use for brute force attacks.
If you prefer using GUI instead of terminal, you can install all these packages from your browser. Open a browser on your machine and go to http://katana.wtf:

The same packages that are available with CLI, can be installed from the browser. So it does not really matter what method you will choose. Let’s continue our tutorial by installing everything from terminal. Firstly, let’s get a vulnerable app, for example, DVWA:
katana install dvwaAfter a moment, Katana should start an automated script that launches the Docker and creates a container. As a result, you should be able to start it:
katana start dvwaOpen your browser and go to http://dvwa.wtf. You should see a running DVWA:

After the installations vulnerable applications are locally, so it can be accessed by respective hostnames:
- DVWA – http://dvwa.wtf
- Amoksecurity – http://amoksecurity.wtf
- … and so on
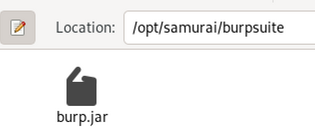
Now as we already have a target, we need a weapon to attack it. Let’s install Burp Suite.
katana install burpsuiteNow as this is a tool, you can’t start it with the katana. After the installation Burp Suite is located at the /opt/samurai/burpsuite. Open a file manager, navigate to the location, and start the burp.jar file:
Now you just have to plugin the proxy in a browser, and you can start hacking!
Final Words
If you are dedicated to become a great bug bounty hunter, SamuraiWTF is resource you should use. At first it is much better to train in a closed environment than on bug bounty platforms. In this way you will better understand why one or another component is vulnerable. You will have a target that is knowingly vulnerable. So, it will be easier to learn, compared to using targets of bug bounty hunting platforms where thousands of people are participating.
And of course, be aware that being a samurai is a prestige, the name talks for itself. But before that, you must train in silent and later let your actions speak for you.

Highly passionate about cyber security (penetration testing, bug bounty hunting, cybersecurity in general), and blogging. I am experienced in vulnerability assessments, penetration testing, various security audits, had worked with various clients, most of them were in finance sector.
CompTIA Security+, CEH, CEH Practical, CEH Master, and OSCP certified.

